The UK cyber skills gap is widening. What it means for hiring in 2026.

11,200 unfilled Cyber Security positions. 49% of organisations short on capability. The story isn't that there's a skills gap. It's that the response model hasn't kept up with the size of it.
The Gov.uk Cyber Security Skills in the UK Labour Market report continues to make uncomfortable reading. The most recent edition puts unfilled Cyber Security positions at 11,200, with 49% of UK organisations reporting a shortage in basic technical Cyber Security skills against current need. 33% report a shortage at advanced level. The pattern, year on year, is the same: the gap widens faster than the supply pipeline can close it.
What's changed in 2026 is that the response on the buyer side has finally started to shift. The historical default – post a job, wait six months, hope the right person arrives – is being quietly retired. In its place, in-house teams are using a mix of embedded partners, Statement of Works delivery and faster contract supply to keep the programme moving while permanent hiring catches up.
Where the gap is sharpest
The shortage is not evenly distributed. Across our pipeline and the wider market data, four disciplines carry the bulk of the unfilled demand:
- Security Architecture – particularly cloud-native and enterprise-scale architects who can hold a transformation programme together end to end.
- SOC operations – L2 and L3 analysts, SOC engineers and threat intelligence specialists. Junior SOC supply has improved; senior supply has not.
- Cloud Security – AWS, Azure and GCP security specialists with hands-on experience of CSPM tooling, IAM at scale and DevSecOps integration.
- GRC and security leadership – CISOs, deputy CISOs and senior GRC consultants able to translate technical risk into board-level conversations.
These are the roles that boards expect to be filled. They are also the roles that take the longest to land. The pattern is structural: the people best placed to take them are already engaged, somewhere, on something else.
Why the traditional model has broken
For a long time, the standard approach was a permanent hire, run through a generalist recruitment partner, with contract resource bridging the gap. That model assumes two things: that the right people are visible to the market, and that you have time to wait for them.
Both assumptions are now wrong.
- The senior cyber population is not visible to the market. The professionals you actually want are already in long-cycle engagements, embedded in transformation programmes, or working through trusted networks. They do not respond to job board adverts.
- Boards no longer give programmes six months to staff up. The cyber risk register is updated monthly. Unfilled critical roles appear in board papers as exposures, not as recruitment metrics.
What in-house teams are doing instead
The teams that are still moving forward in 2026 have shifted to a blended model. The shape varies by organisation, but the components are consistent:
- Embedded capability partners who carry the relationship over years and can mobilise the right specialist within days, not months.
- Fixed-price Statement of Works engagements for defined outcomes – architecture reviews, SOC builds, cloud security uplifts – where the supplier carries the delivery risk and the team comes pre-assembled.
- A rolling permanent pipeline that runs alongside, not in place of, contract supply – so the team grows steadily without programme work stalling.
The common thread is honesty about scale. No single recruitment channel will close an 11,200-role national gap. The teams that staff well are the ones that stop trying to source everything one CV at a time and start treating cyber capability as something to be partnered for, not just hired.
What this means for hiring leaders
Three practical shifts are worth making before the next budget cycle:
- Stop measuring time-to-hire as a single number. Measure time-from-brief-to-on-site, broken out by engagement type. Permanent hires will always be slower; contract and SoW should not be.
- Move at least one recurring requirement (SOC second-line, cloud security, architecture support) onto a partnered model. Single-supplier delivery saves more time than incremental candidate sourcing.
- Make security clearance status part of the workforce plan, not an afterthought. The cleared population is the slowest-moving slice of the market.
The skills gap is not closing in 2026. The question is whether your operating model is built for that reality, or whether it is still pretending the next great hire is around the corner.
Talk to us about closing the capability gap →
Sources & further reading
Want to talk about this? Get in touch →
All insights →More from Market Insight
 Market Insight
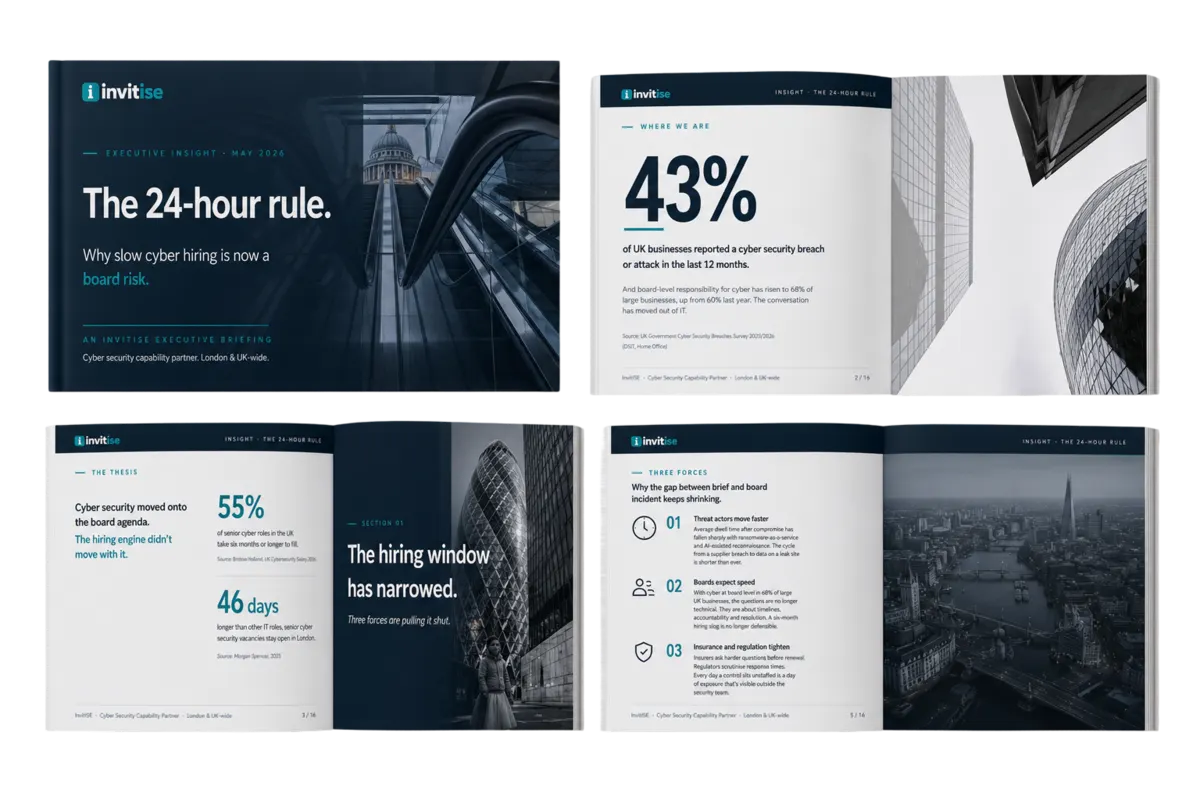
Market InsightThe 24-hour rule: why slow Cyber Hiring is now a board risk
Cyber Security has moved onto the board agenda. The hiring engine hasn't moved with it. Here's why the gap between brief and on-site is now the metric that matters.
 Market Insight
Market InsightFrom day rates to outcomes: the shift to fixed-price cyber in 2026
Joint & Several Liability rules landed in April. End clients no longer want to assess IR35 status on every contractor. Fixed-price Statements of Work are becoming the default. Here's what genuine outcome delivery looks like.
_1778603447189-DGEkYDPq.png)